IT'S THEIR WORD AGAINST THEIR SOURCE CODE - TIKTOK REPORT
In our original report our head security engineer, Thomas Perkins, has revealed the excessive data collection of TikTok and that the app connects to mainland China based infrastructure. (We note that we put all of our research to TikTok for comment and verification. They refused to go on the record about the details of their China based infrastructure.)
Our paper was also featured in the Australian Financial Review and der Spiegel.
Executive Summary
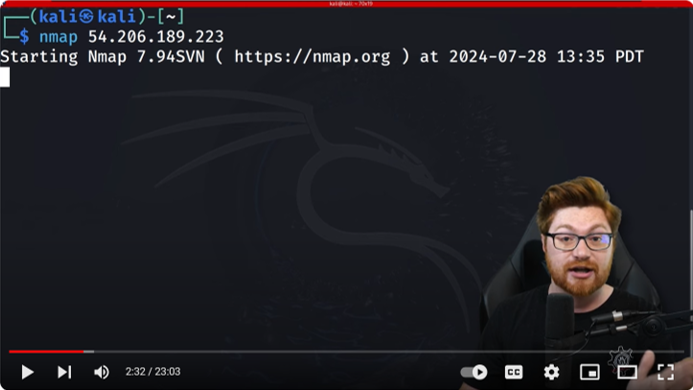
This report is a technical analysis of the source code of TikTok mobile applications Android 25.1.3 as well as IOS 25.1.1. Analysis of the Android application was performed using a Galaxy S9 cell phone. Internet 2.0 conducted static and dynamic analysis of the source code between 01-12 July 2022. This report aims to analyze TikTok device and user (customer) data collection. Prepared by Internet 2.0, this report is for policy makers and legislators to make evidence based decisions. TikTok is a dominant social media application and is the 6th most used application globally with forecasted advertising revenues in 2022 expected to be USD12 billion. In our analysis the TikTok mobile application does not prioritize privacy. Permissions and device information collection are overly intrusive and not necessary for the application to function. The following are examples of excessive data harvesting.
• Device Mapping. The application retrieves all other running applications on the phone. TikTok also gathers all applications that are installed on the phone. In theory this information can provide a realistic diagram of your phone.
• Location. TikTok checks the device location at least once per hour.
• Calendar. TikTok has persistent access to the calendar.
• Contacts. TikTok has access to contacts and if the user denies access, it continuously requests for access until the user gives access.
• Device information. TikTok has code that collects the following device detailed information on Android. Wi-Fi SSID, Device build serial number, SIM serial number, Integrated Circuit Card Identification Number (this is global unique serial number that is specifically tailored to your SIM card), Device IMEI, Device MAC address and Device line number.